
- Application Services
- Next-Gen App Development
- Mobile Application Development
- Modernization
-
-
- Integration ServicesGet seamless integration of various 3rd party services or existing systems for smooth operations of your mobile apps
- Cross PlatformsExcellent user experience and functionality of native apps with multi-platform compatibility
- Legacy System Modernization ServicesLegacy system modernization empowers organizations so that they can work more efficiently and intelligently.
-
-
- DevOps
- Software Testing
-
-
- AI Enabled TestingLeverage AI for testing the quality of your software products
- Functional TestingAutomated Functional Testing for improved quality & faster go-to-market
- STQC CertificationQuality, Excellence, and Innovation – The Hallmarks of Suma Soft
- Performance TestingEliminate performance bottlenecks of business-critical apps to run under expected, peak loads
-
- Scriptless Automation SolutionsFast, reliable, and easy testing with our “Ready-to-Deploy” automation framework
- Devops TestingOptimize testing in CI/CD pipelines for greater agility, efficiency, and quality
- AA CertificationEmpaneled Certifier for Account Aggregator (AA) Ecosystem
- ABDM Ecosystem Sandbox Exit ProcessWe Certify Your API for ABDM Sandbox Integration And Exit Process
-
-
- AI/ML Services
- AI/ML ServicesStay ahead of the curve with our advanced AI/ML capabilities
- Data Engineering ServicesDrive data-driven decision-making with our agile and customizable data engineering solutions
- Software Product Engineering ServicesTransform your concepts into market-leading products with our strategic product engineering approach
- VaniePartner with Us for Innovative Web App Solutions!
- Indiastack
- Account AggregatorGet certified using Daksh DEPA Validator to go live on the AA network.
- Ayushman Bharat Digital Mission (ABDM)Get certified using Daksh DEPA Validator to go live on the ABDM network.
- Beckn Protocol ImplementationImplement Beckn protocol to go live on India Stack network.
- ONDC CertificationGet certified using Daksh DEPA Validator to go live on the ONDC network.
- O Rickshaw Pune’s First ONDC Mobility App
- Business Services
- Business Process Management
-
-
- Healthcare BPO ServicesRound the clock coverage for most critical industry
- Logistics BPO & Supply Chain ManagementSmarter supply chains Built for today and ready for tomorrow
- Data Entry ServicesEnsure the accuracy and security of your data with Suma Soft
- Underwriting support servicesStreamline underwriting processes , increase accuracy, reduce risk with expert support services.
- Finance and Accounting ManagementImproving Account Payable and Receivables Through Artificial Intelligence
-
- Logistics BPO ServiceOptimize logistics with efficient operations, reduced costs, and our improved visibility.
- Customer Support ServicesSmart use of technology makes all the difference in CX
- REIT Management ServicesProductivity for You. Transparency for Your Investor
- OCR Outsourcing ServicesAchieve faster, accurate and reliable data capture with OCR outsourcing solutions.
- Claims ManagementState-of-the-art technology to assist in responding to rapidly-evolving claim situations
-
-
- Tech Support
-
-
- Desktop SupportResponsive, Day-to-Day Tech Assistance
- Network SupportCreate a comprehensive network security strategy for protecting the enterprise end-to-end
- Active Directory SupportMinimize the risk of disrupting critical business apps while optimizing the performance of MS infrastructure
- Microsoft Exchange SupportStay on top of imminent threats to achieve a glitch-free network with rapid Microsoft Exchange support
-
- L1 & L2 SupportOptimize performance with round-the-clock technical support cater to your business goals
- Remote MonitoringKeep your IT systems running smoothly and ensure the stability and security of your IT environment for the workforce
- NOCGet unrivaled NOC services & scale immediately to enhance your bottom-line profitability with 24*7 services
-
-
- Hyperautomation
-
- Cyber Security
-
-
- AssessmentTest your applications and networks to identify & fix vulnerabilities exposing your sensitive assets
- Cloud SecurityIntelligence and expertise providing a new level of cyber-immunity
- Managed SecurityComprehensive security architecture with flexible enforcement for advanced protection
- Digital ForensicsEmpower your organization to access, manage and leverage Digital Data
-
-
- ServiceNow
- ServiceNow Managed ServicesOngoing ServiceNow support and optimization for peak performance.
- ServiceNow Integration ServicesOngoing ServiceNow Integration Services
- ServiceNow Implementation ServicesExpert ServiceNow implementation for customizable business solutions.
- ServiceNow Migration ServiceAchieve seamless platform transitions with smooth ServiceNow migration.
- ServiceNow Consulting ServicesStrategic ServiceNow consulting for optimal platform utilization.
- ServiceNow ITBM ImplementationImplement ITBM for strategic IT planning and execution.
- ServiceNow ITSM Implementation ServicesPlan and streamline IT service management with expert implementation services.
- ServiceNow Chatbot DevelopmentEnhance user experience with intelligent ServiceNow chatbot solutions.
- ServiceNow CSM ImplementationImprove customer service with efficient ServiceNow CSM implementation.
- ServiceNow GRC ImplementationManage governance, risk, and compliance with ServiceNow GRC.
- ServiceNow Security OperationsStrengthen security posture with ServiceNow security operations management.
- ServiceNow IT Operations Management ServicesOptimize Your IT Operations with automated workflows and efficient service delivery.
- ServiceNow HR Service DeliveryEnhance employee experiences with automated HR service management.
- ServiceNow Financial ManagementStreamline financial operations and improve decision-making with ServiceNow.
- ServiceNow Asset Management ServicesControl IT assets, reduce costs, and ensure compliance with ServiceNow Asset Management.
- Project Portfolio Management ServiceNowPrioritize projects and manage resources for successful delivery.
- Resource Management with ServiceNowStreamline resource allocation for project efficiency and success with ServiceNow Resource Management.
- Business Process Management
- Digital
- Cloud
-
-
- Cloud App Development ServicesGet high security, efficient performance, and excellent operations with cloud apps
- Cloud Testing ServicesDelivering highly polished solutions to help you reduce costs and meet deadlines
- Cloud Migration ServicesA secure cloud single sign-on solution that IT, security, and users will surely love
-
- Enterprise Mobility
- CRM
- Microsoft Dynamics 365 ServicesStreamline business processes with superior BI, automation, and key customer insights
- Custom CRM Development ServicesDigitize processes, enhance everyday managerial activities and engage more customers
- Salesforce Consulting ServicesTransform Your Business with Expert Salesforce Guidance – Elevate Performance and Drive Growth!
- Salesforce testing servicesAchieve end-to-end automation for Salesforce testing
- E-Learning
- Collaboration
- Dusmile Platform
- Cloud
- Insights
- Industries
- Industry We Serve
- Banking And FinanceAccelerate your journey with fintech innovation to reshape customer experience
- GovernmentFully-managed environment for Government, Built for security and compliance
- E-CommerceBest-of-breed technologies to enhance CX and increase revenue to maximize business needs
- E-LearningReimaging education – from remote to hybrid learning
- Logistics & DistributionChanging the landscape of supply chain management
- AutomotiveRevolutionizing automotive development for the digital future
- HealthcareDelivering better experiences, better insights, and better care for better health
- ManufacturingLeverage our deep expertise to modernize your manufacturing and industrial technologies and processes.
- Industry We Serve
- About Us
- About Suma Soft
- HistoryDecades of experience and expertise matched with dedicated professionals.
- LeadershipA leadership that drives Suma Soft to meet its overall goals.
- CertificationsOur recognition as a trusted technology company for orchestrating a successful business transformation
- Our PartnersBringing together the best technologies and practices to offer a prosperous digital future
- Annual ReturnSuma Soft’s Yearly Financial Annual Return Report
- About Suma Soft
- Careers
- Contact Us
API Penetration Testing to Address the Wide Range of API Vulnerabilities
August 24, 2022

List of Top 10 API Vulnerabilities
What is API?
Before going into the details of “API Penetration Testing,” let us first understand what API means and its significance. API stands for Application Programming Interface, API essentially facilitates communication between computers and more specifically between independent computer programs or software. Technically termed a “Software Interface,” API is important in software and application development. APIs play a significant role in the development of Mobile applications, web applications, and other computer programs.
API Documentation and API Specifications
The word API is often used interchangeably with two related, but distinct attributes called API Documentation and API Specifications. API document is described as a standard reference manual for developers that outlines the rules of how to use an API. API document tells a developer how to use the API. The API specifications, on the other hand, are a resource that explains how a particular API behaves, how to link with different APIs and what results to expect from it.
Unlike User Interfaces, APIs are not used directly by average humans [other than computer programmers], though they engage with APIs without being aware. The immense functionality of the APIs does come with a price – SECURITY. This is where the topic under consideration in this article, “API Penetration Testing,” comes into the picture.
What is API Penetration Testing?
API Penetration Testing is a comprehensive methodology that tests the overall security features of the APIs. It is an ethical hacking process deliberately deployed to ascertain and evaluate the security aspects of the API. During API Penetration Testing, the possible vulnerabilities in the API are exploited by ethical hacking methods and reported to the developers. Developers then fix these issues strengthening the API further to prevent unauthorized access and data breach.
API Abuse
It is one of the most common threats to web applications. API Abuse is the wrong handling of the APIs with the intent of gaining unauthorized access, scraping critical business data, and launching DDoS attacks on the server. API abuse can severely disrupt the smooth functioning of your IT infrastructure. And hence API Penetration Testing is of paramount importance to avert the possible abuse of APIs.
API Penetration Testing is a very complex task that calls for a sound understanding of various tools needed to check the vulnerabilities in the APIs. Here are a few tools that cyber security service providers employ.
Burp Suite – Offers scalable automated scanning as well as manual testing. Used by cyber security experts for manual penetration testing. Rated 4.3 out of 5 by Peerspot.com.
Postman – Tests HTTP requests with the help of a user-friendly graphical UI. Cybersecurity experts use it to obtain different responses and then validate them. Postman API testing tool Allows you to create different testing environments and is fast too.
ZAP Proxy – This API testing tool understands API formats like JSON & XML and is used by cyber security experts to scan APIs. Peerspot.com has rated OWASP ZAP at 7.2 out of 10.
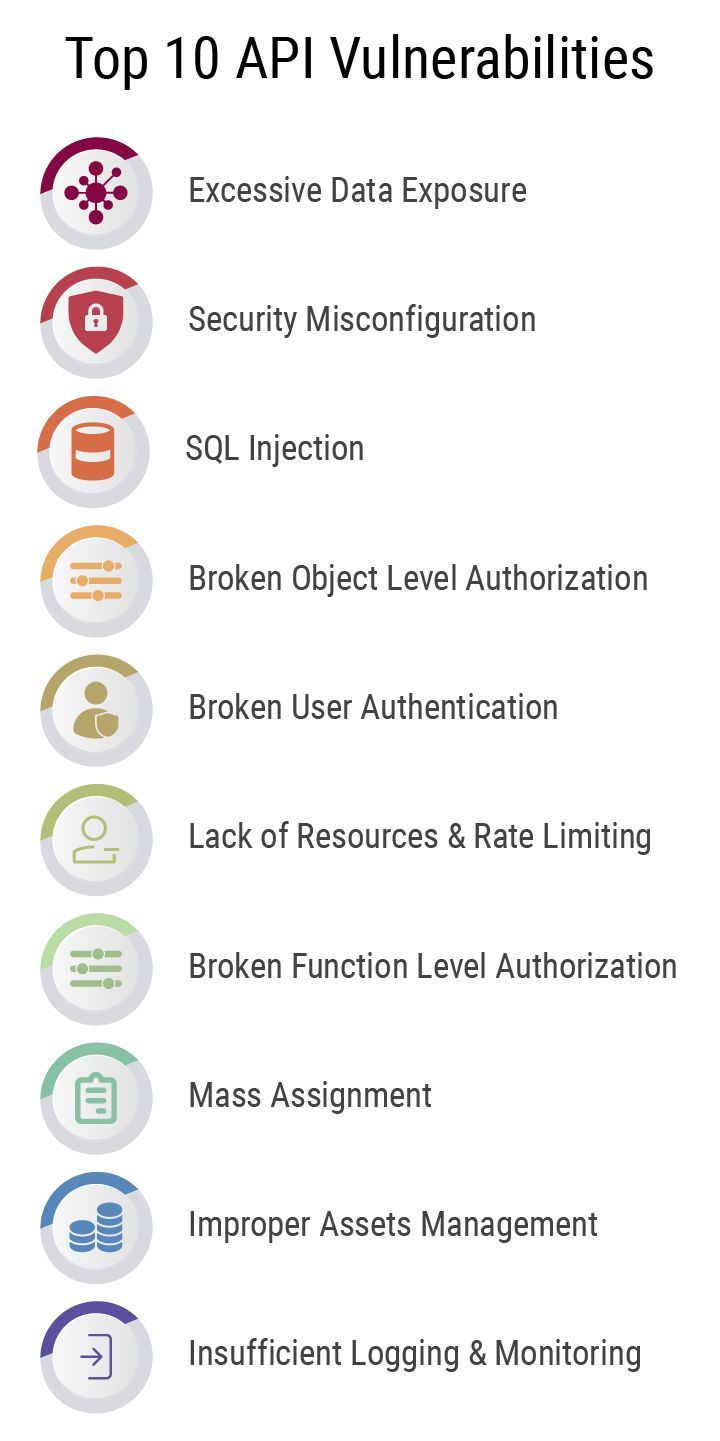
Top 10 API Vulnerabilities
API Vulnerability 1 – Excessive Data Exposure
This situation arises when the API returns sensitive data through techniques like API Response and Request calls. An API abuse can manifest when developers and programmers might inadvertently expose objects, disregarding individual security. This data may contain personally identifiable information like email ids, phone nos., etc. The best way to prevent API abuse in this fashion is to never rely on the client to filter sensitive data.
API Vulnerability 2 – Security Misconfiguration
This scenario consists of various parameters such as misconfigured HTTP headers, incomplete ad-hoc configurations, insecure APIs, open cloud storage, insecure default configuration, error messages showing sensitive information, etc. The abuse of this API vulnerability can be avoided by adopting the best practice of following an API life-cycle that repeatedly hardens the process, resulting in the fast and smooth deployment of a properly locked environment.
API Vulnerability 3 – SQL Injection [SQLi]
The method is a form of code injection used by hackers to target data-driven applications. SQL injections, Command injections, and NoSQL injections exploit the security weaknesses in the applications & programs. These cyber attack methods send data from unknown sources to an interpreter through a query or command. Injection vulnerabilities are common in SQL, LDAP (Lightweight Directory Access Protocol), NoSQL queries, OS commands, Object-Relational Mapping (ORM), and XML parsers. These vulnerabilities can be easily identified when a programmer scrutinizes the source code.
Attackers often deploy scanning & fuzzing techniques to exploit the vulnerabilities in the applications and programs to gain unauthorized access to sensitive information. The key to avoiding SQL injection is to keep the data distinct from commands and queries. Maintaining a single, actively maintained library for data validation is also recommended.
API Vulnerability 4 – Broken Object Level Authorization
Here the APIs have a propensity of exposing the endpoints that handle object identifiers, which can result in a wide attack surface Level Access Control issue. To avoid this scenario, developers must inspect all the functions that access a data source with user input. Put in place a fail-proof authorization mechanism that takes into account the hierarchy & user policies.
API Vulnerability 5 – Broken User Authentication
This issue is related to an incorrectly implemented authentication mechanism. This weakness allows attackers to compromise authentication tokens or exploit the flaw in implementation by assuming other users’ identities – temporarily or permanently. This issue compromises the system’s ability to identify the client/user, and overall API security. The API abuses arising from this vulnerability can be avoided by checking the flows to authenticate the APIs. Developers must know all the flows to authenticate to the API.
API Vulnerability 6 – Lack of Resources & Rate Limiting
It is time and again observed that APIs fail to impose a cap on the quantity or size of the resources a client/user can request. The lack of such restriction has an impact on the performance of the API server, which can lead to a Denial of Service (DoS) situation. These unchecked restrictions can also inadvertently facilitate attack methods such as brute force, which takes advantage of the authentication weakness. To avoid the API abuse with this technique, it is suggested to use Dockers to restrict the number of processes, restarts, CPU, memory, and file descriptors.
API Vulnerability 7 – Broken Function Level Authorization
A big organization has several levels of hierarchy that can be categorized into several groups with specific roles and functions. These types of authorization flaws become apparent when there is no clear distinction between regular & administrative functions. It is recommended that the application have an authorization module that is easy to analyze and is invoked from all the business functions.
API Vulnerability 8 – Mass Assignment
Mass Assignment vulnerability occurs when there is no proper filtering based on the allowlist of the data [like JSON] provided by the client, bound with data models. In this vulnerability, the attackers modify the object’s properties, which they are not authorized to do. They employ methods such as guessing the object properties, reading the document, investigating endpoints of other APIs, and exploiting the additional object properties provided in request payloads. To avoid the APIs being abused in this fashion it is recommended to prevent the practice of using functions that bind the client’s input to code variables or internal objects.
API Vulnerability 9 – Improper Assets Management
Compared to traditional web applications, APIs have a tendency of exposing more endpoints. And hence thorough documentation of APIs gains paramount importance. Proper host, API versioning & API inventory also help in preventing API abuse pertaining to deprecated API versions and also exposed debug endpoints. To prevent API abuse it is recommended to maintain an inventory of all API hosts. And also, thorough documentation of the essential features needs to be undertaken. Pay more attention to the API Environment. Assess which users have network access to the API host and the API version.
API Vulnerability 10 – Insufficient Logging & Monitoring
The harmful combination of lack of proper monitoring & logging and improper integration with incident response encourages hackers to attack newer systems persistently. The attackers can abuse the API vulnerability to extract data or destroy it. Study shows that the time taken to detect a data breach is more than 200 days, and in most cases, the data breach is detected by external parties and not by the internal monitoring processes. To prevent this type of API abuse, it is recommended to maintain a log of events that include input validation errors, incidents of denied access & failed authentication attempts.
Author
Saeel Relekar is a Certified Ethical Hacker and an Information Security Analyst at Suma Soft. Suma Soft is a market leader in Cyber Security Services and provides comprehensive security solutions to safeguard enterprises.
Recent Posts
- DevOps in Software Product Engineering: Streamlining Development and Operations September 10, 2024
- Accelerate Your Business with Our Data Engineering Solutions: A Case Study August 20, 2024
- The Role of Cloud Computing in Modern Data Engineering Solutions June 25, 2024
- Why 70% of Enterprises Are Choosing Hybrid Apps and How They Benefit May 24, 2024
- How Building a Native App Can Increase Customer Engagement by 3X May 20, 2024
- What Competitive Advantages Do PWAs Offer Over Traditional Mobile Apps? May 16, 2024
- 5 Must-Have Features for Enterprise-Level iOS Apps May 14, 2024
- 5 Ways to Supercharge Your Android App with AI and Machine Learning May 8, 2024
- Comparing Traditional ETL vs. Modern Data Engineering Approaches April 24, 2024
- Can Outsourcing E-Commerce Customer Service Actually Drive Sales and Brand Loyalty? April 10, 2024